HTTP Proxies
Introduction
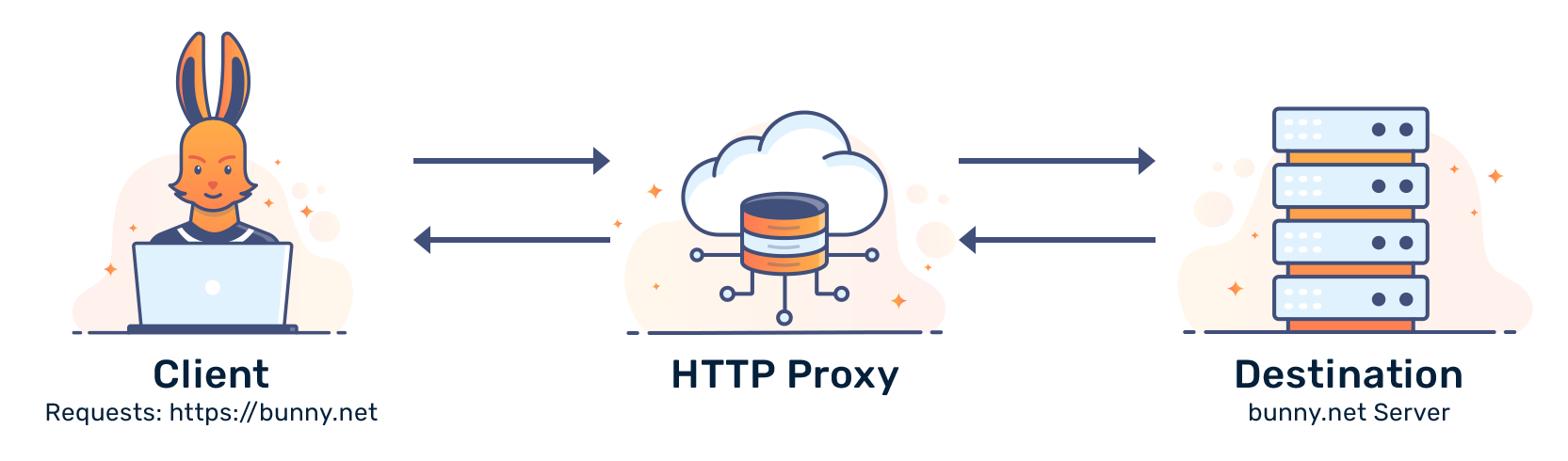
HTTP Proxies are HTTP servers that sit between you and a destination. An HTTP proxy takes requests from a client, forwards the request to a server, then proxies the reply back to the client. This kind of proxy is sometimes called a forward proxy, since it forwards requests to the server.
Here's an example of a request:
Benefits
HTTP proxies can perform actions like content blocking and compression.
Compression can accelerate requests from a destination by reducing the size of the data being sent. Content-blocking can remove advertisements, or apply filters to a child's internet access.
Drawbacks
Unfortunately, HTTP proxies aren't designed to forward HTTPS (secure) data. Such requests break the chain of trust between a client and a server. Data isn't secure when sent through a forward proxy. Proxies must decrypt and re-encrypt data using a local/self-signed certificate.
This also means that HTTP proxies are designed to transmit data in plain text.
Conclusion
HTTP proxies offer negligible performance benefits and are (essentially) a middleman for data. They should not be used for secure data, as the vast majority of public HTTP proxies don't support HTTPS traffic.
