Email Obfuscation
Why are email addresses obfuscated?
Email addresses are common targets for spam, phishing attacks, and malicious crawlers. While there are many ways to obfuscate addresses from marketers or bots, no method is perfect. On top of this, usage of simple obfuscation techniques often results in a worse user experience. It should be balanced with more user-friendly techniques (that are less effective protection against spam).
Email obfuscation is a simple concept that can be difficult to balance between bot-prevention and the overall user experience.
How email addresses get obfuscated
As mentioned previously, there are many ways for Email Obfuscation to happen:
1) Putting email addresses into images
This is a simple method of obfuscation — essentially, a website owner can embed their email address into an image that a bot cannot read. Unfortunately, newer AI neural networks can defeat this type of obfuscation. Users also have to read text from an image, resulting in both accessibility and user experience issues.
2) Text-based obfuscation
Text-based obfuscation involves putting email addresses in a human-readable format that is still hard for a crawler to read. For example, if a webmaster wishes to place support@bunny.net on their website, a potential deterrent would be to write support(at)bunny(.)net or some variation. Similar to the previous technique, users lose out again as they cannot easily copy an address.
3) JavaScript-based obfuscation
Using JavaScript, addresses can be placed onto a page dynamically to hide them from bots. For example, an easy way to obfuscate email addresses on a page is to set an ID for the HTML tag containing the email address and having the email encoded in base64:
<p>
I am available at the following email address: <span id="email"><noscript>JS is required to view this address.</noscript></span>
</p>
Now, when a legitimate browser loads the website, the following code is executed:
<script type=”text/javascript”>
var email = "c3VwcG9ydEBidW5ueS5uZXQ="; // support@bunny.net
document.getElementById("email").innerHTML = atob(email);
</script>
… and for regular users, an email address (that can be copied) appears:
I am available at the following email address: support@bunny.net
While imperfect, this solution is the most user friendly of the four listed methods. Users don't have to read text from an image or remove placeholders. The only downside to this form of obfuscation is the relative simplicity of decryption: any bot running a fully-fledged browser can easily bypass basic forms of JS-powered email hiding techniques.
4) Captcha-based obfuscation
CAPTCHAs, or user challenges, are typically the least user-friendly solution to hide contact information. They usually look like this:
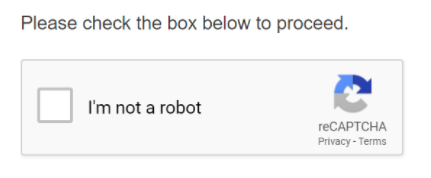
Other variations include scrambled text or auditory CAPTCHAs. Another major issue is the existence of services that can solve CAPTCHAs automatically; not only do CAPTCHAs make a user experience far worse, they can end up being equally as insecure as any other option.













