What are Cross Site Scripting (XSS) attacks?
Introduction
 Cross-site scripting (XSS) attacks are a form of attack that aims to run unauthorized JavaScript (JS) on other clients. When a website is vulnerable to an XSS attack, an attacker can send a snippet of code to the server, usually through a vulnerability in HTML/JS sanitization. The snippet of code is then executed on other client browsers.
Cross-site scripting (XSS) attacks are a form of attack that aims to run unauthorized JavaScript (JS) on other clients. When a website is vulnerable to an XSS attack, an attacker can send a snippet of code to the server, usually through a vulnerability in HTML/JS sanitization. The snippet of code is then executed on other client browsers.
For example, if YouTube comments were vulnerable to XSS attacks, an attacker could gain access to thousands of accounts instantly and post comments on each user’s behalf.
The two most common attack vectors are:
- Non-persistent, reflected XSS Attacks
- Persistent, stored XSS Attacks
Reflected XSS attacks
Reflected XSS attacks operate on the principle of temporary data. For example:
https://youtube.com/watch?v=<script></script>
In this example, there is no actual vulnerability. If it did exist, the page would need to print a user's input for the video URL.
As seen in the example above, XSS attacks are pretty simple. They require little-to-no effort on the part of an attacker, are hard to trace, and often mislead even tech-savvy users. These attacks are effective because you might not think twice about clicking on a trusted website such as Google, YouTube, or Wikipedia. XSS attacks are particularly effective when sent through messaging platforms where the full links are often shortened.
Persistent/stored XSS attacks
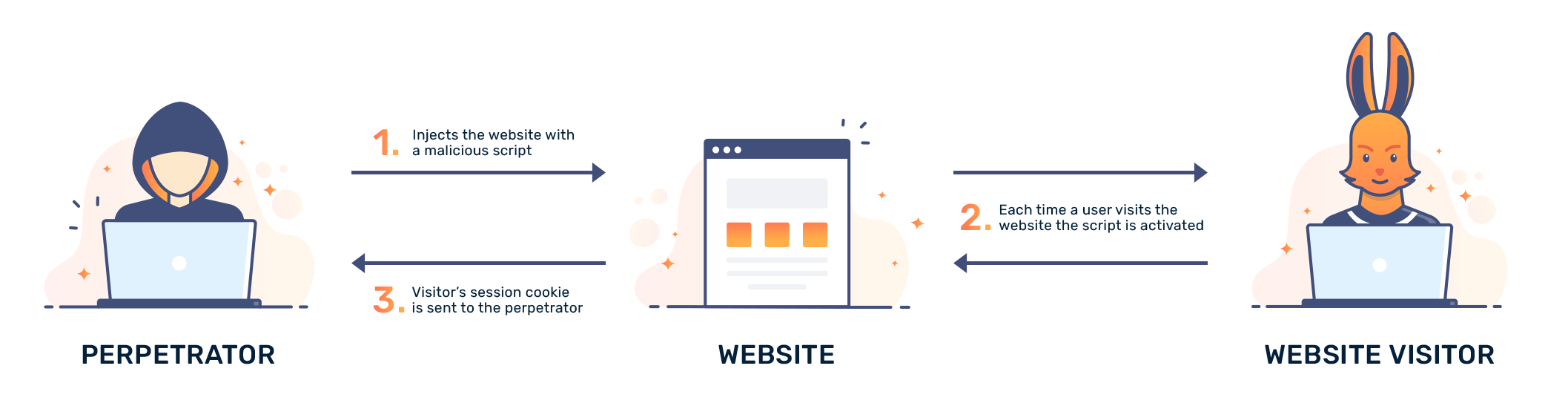
Persistent XSS attacks involve attacking a vulnerable website. In particular, snippets of JavaScript can be sent to a victim's server. Once the vulnerable server ingests the data, it can do a few things. If the data is only shown back to the user, then the attack is of limited use. The attack becomes particularly dangerous when the code is placed on a publicly-accessible page. An attacker can scrape cookies, account information, and personal information.
Simply put, webmasters should always be wary of any user input. Assuming user input isn't sanitized, anything can be sent to a server. Anything can be sent to a server if user input isn't sanitized.
Example
If you write on a blogging platform that doesn't remove JS or special characters, it might be vulnerable to snippets of code. For example, you could add this snippet to the biography section:
<script type=”text/javascript”>
alert(“XSS!”);
</script>
Applied to a vulnerable website, this script makes the biography display the alert message: "XSS!"
Conclusion
While there are other forms of XSS attacks, the two most common include reflected and stored XSS attacks. Attacks can proceed after a victim visits a compromised page, or clicks on an altered link. Regardless of what an attacker does, it's important for users to avoid clicking on content that they don't trust. It's a shared responsibility, a zero-trust approach to user input should be taken with any secure web application.













