What is a Honeypot trap and what are high vs low interaction honeypots?
Introduction
The worldwide web is constantly evolving and so are attacks from malicious actors. In order for companies or individuals to detect attacks in advance, they use a technique known as honeypots.
Honeypots are, fundamentally, traps. They lure, and capture, the activities of malicious actors that could potentially attack other critical infrastructure/servers in the future. There are typically two types of traps:
- Research honeypots
- These honeypots monitor weaknesses that are currently being exploited and report their findings such that webmasters/programmers are aware of current threats
- These bait traps help track botnets or other malicious software across the web
- Production honeypots
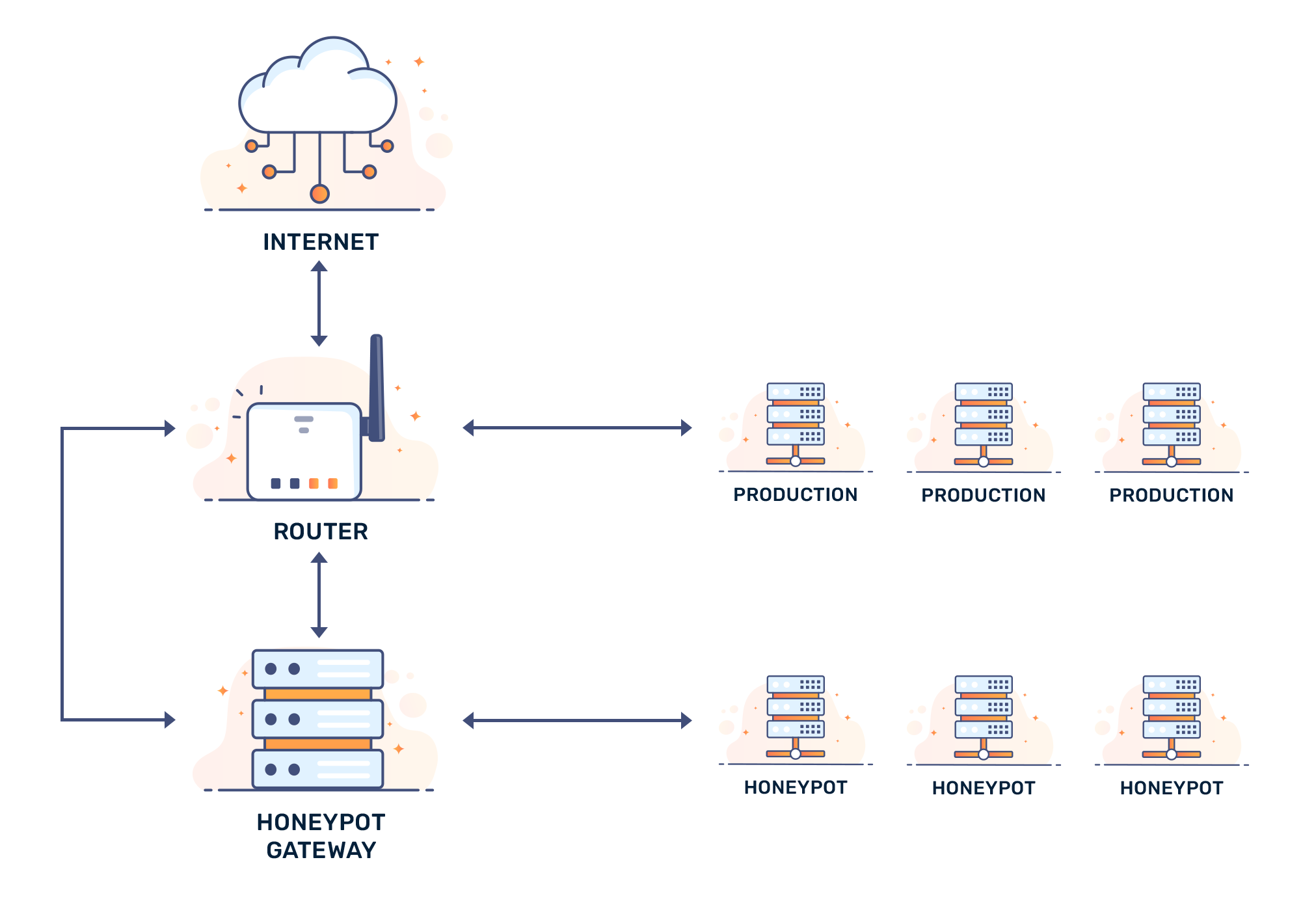
- These honeypots are a fake target set up to distract hackers from real, valuable data within the network
Variations of honeypots
There are many variations of a honeypot, such as:
1) Malware honeypots
Malware honeypots are designed to trap (i.e. detect) malware. For example, a decoy API server could be set up to trick an attacker (or automated bot) such that they attempt to steal information by means of malware.
Fortunately, malware honeypots are never connected to a company’s primary infrastructure. The honeypot is most often placed on an external server, away from any critical servers.
2) Spider honeypots
While a spider honeypot does not necessarily search for bad traffic, it does sit and monitor web trends (from browser types to crawler versions). As a side effect, they can track and monitor botnets, the general locations of cyberattacks, to attack vectors.
Since the honeypot is merely set up to listen for these attacks, there is no infrastructure to attack; there is only a server forwarding logs and information to the company or individual that runs said honeypot.
High interaction vs. low interaction honeypots
High interaction network honeypots aim to waste as much of an attacker's time as possible. An attacker who breaches a high interaction network honeypot will see something very similar to a production system. An attacker's actions in the honeypot provide valuable information which is used to create bug-fixes and patches for live applications.
Low interaction honeypots are used to lure automated attackers, like bots and crawlers. With low interaction honeypots, bait is placed away from primary infrastructure. This form of honeypot is used to find vulnerabilities that could grant dedicated attackers access to important information.
Conclusion
Honeypots are a useful tool for hacking prevention. They generate valuable data that can be used to patch out emerging viruses and web attacks — even monitor for SQL vulnerabilities.
From a security perspective, honeypots can also bait attackers away from core applications, which also acts as a defense. With that in mind, honeypots do not replace actual security updates and maintenance. They exist to help create updates.













