APIs sit at the center of almost everything you build today.
They handle authentication, power your frontend, connect your services, and move data between them. Requests are syntactically valid, responses return as expected, and systems stay online. Yet requests still reach your application that don’t belong there.
When something goes wrong, it’s rarely a dramatic outage, but something more subtle. A request your API doesn’t define still slips through, a payload doesn’t match what your application expects, or an endpoint gets called in a way that technically works but was never intended.
The problem is that most security systems are designed to detect what looks malicious. APIs don’t always fail that way. Requests can be completely valid from an HTTP perspective and still violate how your application is supposed to behave.
That gap between what is valid and what is correct is where API abuse happens. We see it constantly at the edge, where traffic looks valid on the surface but doesn’t make sense for the API it’s targeting.
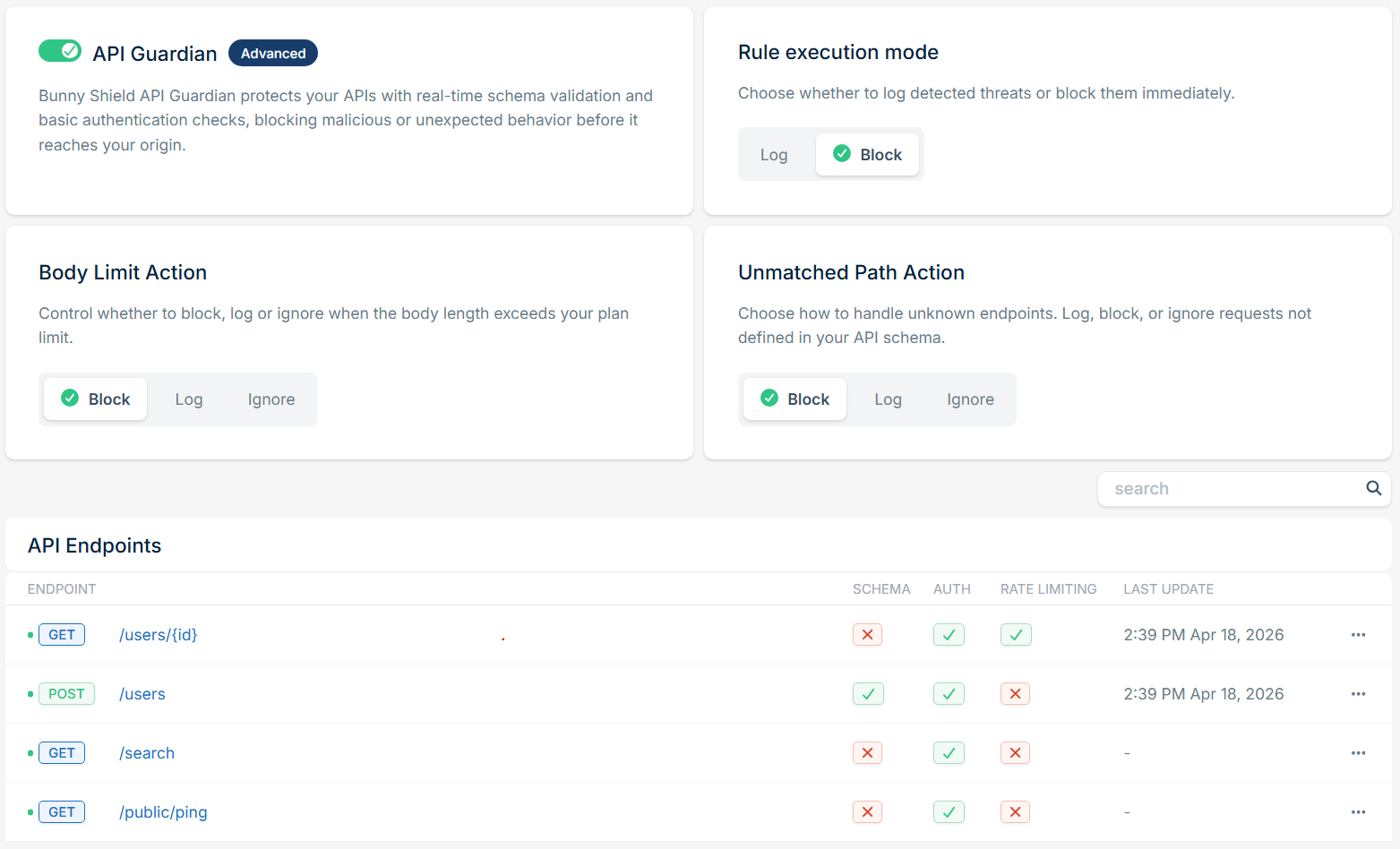
Today, we’re introducing API Guardian, a new layer of Bunny Shield that brings schema-aware protection to your APIs by turning your OpenAPI definition into enforceable validation at the edge.
It builds on everything we’ve shipped with Bunny Shield since launch. WAF, Global Rate Limiting, Bot Detection, and Access Lists control how traffic reaches your application, while Upload Scanning inspects what gets through. API Guardian delivers the final piece we set out to build. It validates requests against what your API is defined to accept and enforces it in real time.
Instead of asking whether a request looks suspicious, API Guardian asks whether it makes sense according to your API contract.
Validate requests at the edge using your schema
API Guardian starts with something you already have: your OpenAPI schema.
When you upload a spec, it becomes an enforceable contract at the edge. Each endpoint is translated into validation rules that run directly inside Bunny Shield’s request security pipeline, so invalid requests can be filtered before they ever reach your origin.
Under the hood, the spec is normalized, schemas are extracted, and references are resolved (internal only) before being compiled into native WAF rules.
API Guardian enforces safety limits at upload time, including a maximum spec size of 2 MB. These limits cover nesting depth, total schema complexity, and regex usage. These guardrails ensure predictable performance and prevent excessively complex schemas from impacting validation at the edge.
Validation covers the full request surface:
path parameters, query parameters, headers, cookies, and JSON request bodies
(application/json
and
*+json).
You can log, block, or ignore requests that don’t match, depending on how strictly you want to enforce your API surface.
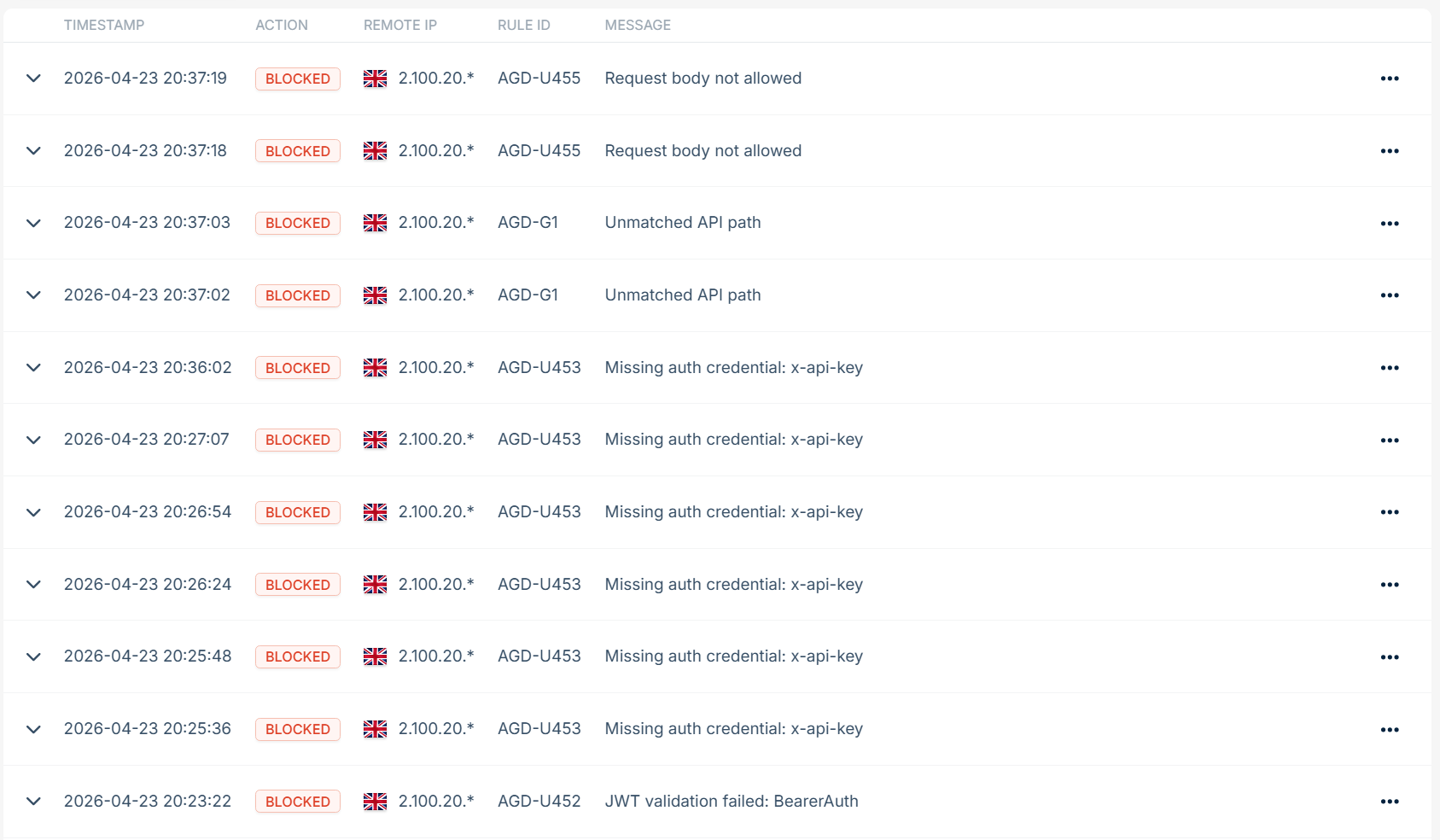
Validation events that result in logging or blocking are recorded in your Bunny Shield event logs, so you can see what is being flagged and why.
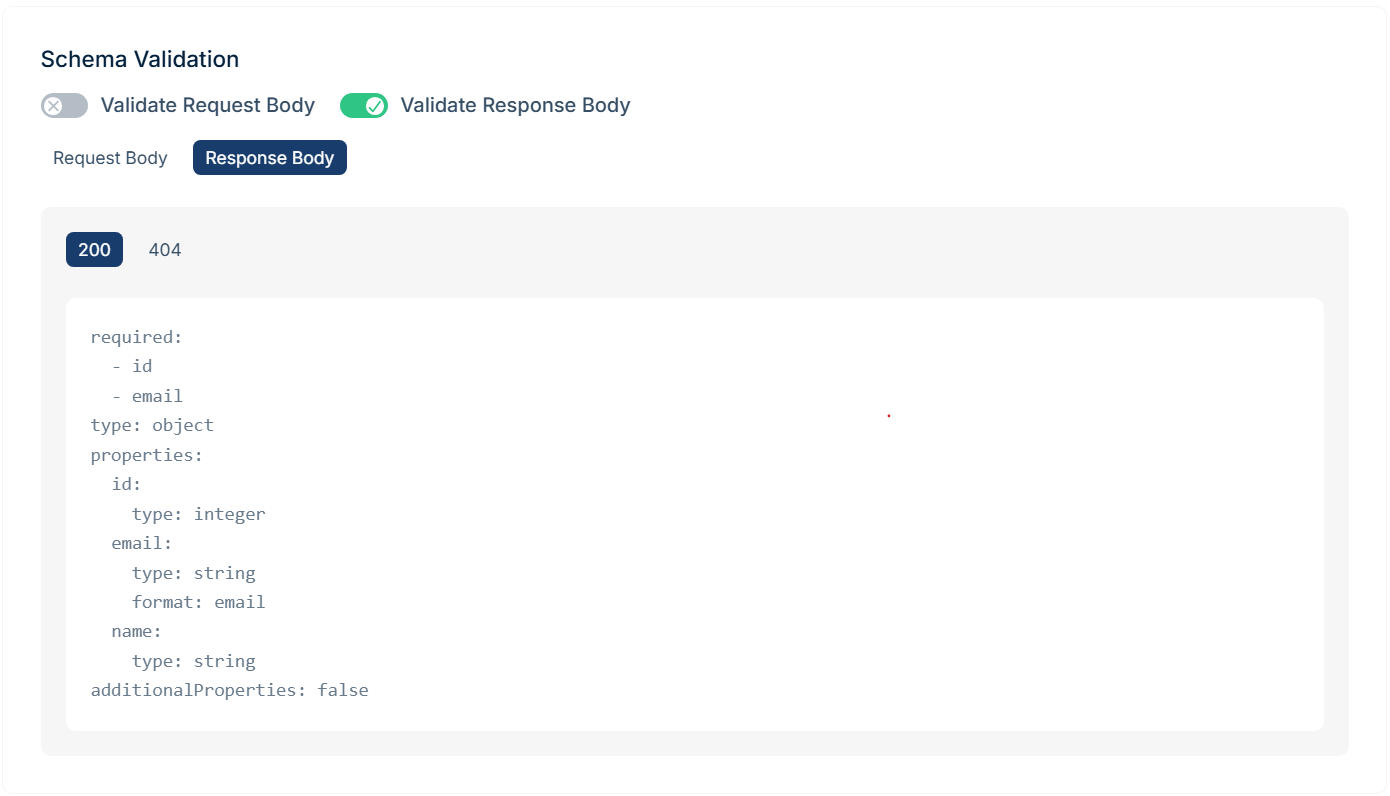
Keep responses aligned with your contract
APIs define both the inputs your system accepts and the outputs it produces.
When requests are malformed or deliberately crafted, responses can behave in unintended ways. Error paths, edge cases, or inconsistent handling can expose fields or data that were never meant to be returned.
API Guardian can validate responses against your schema on a per-endpoint basis. When enabled, responses are checked before they leave your system, helping prevent unexpected or unsafe output from reaching clients.
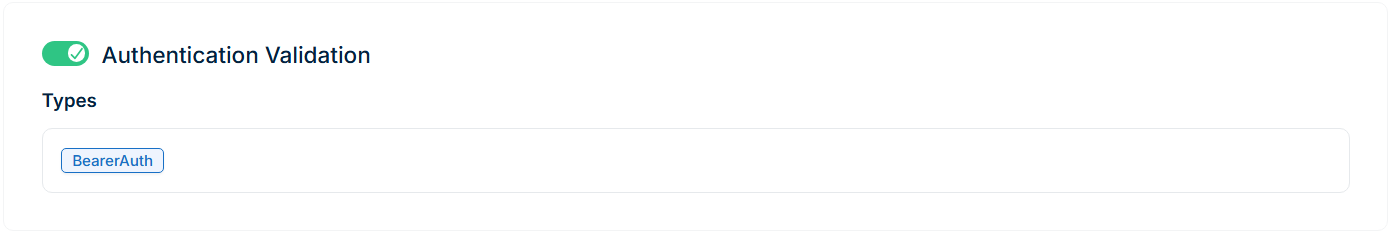
Enforce authentication at the edge
APIs are harder to protect than traditional web traffic because requests often look valid at the protocol level, even when they’re not meaningful for the application.
Most unwanted traffic still fails basic authentication checks. Bot traffic, scanners, and volumetric attacks rarely include correctly formed credentials, and almost never include valid tokens.
API Guardian enforces authentication requirements defined in your schema before requests reach your origin. It supports API keys (headers, query parameters, or cookies), HTTP authentication (Bearer and Basic), OAuth2, and OpenID Connect.
Requests missing required credentials are rejected immediately at the edge, reducing unnecessary load and filtering out a large portion of low-effort attack traffic.
For Bearer tokens defined with
bearerFormat: jwt,
API Guardian performs basic checks such as validating structure and expiration. This allows you to filter out malformed or clearly invalid tokens before forwarding the request, while leaving full authentication and authorization to your application.
For OpenID Connect schemes that use public-key signing, API Guardian can also verify token signatures at the edge. It retrieves the provider’s configuration, resolves the advertised JWKS, and keeps keys updated as they rotate.
Tokens are validated against the expected issuer and signing algorithm before being forwarded. Invalid, expired, unsigned, or tampered tokens are rejected at the edge, ensuring only properly signed requests reach your origin.
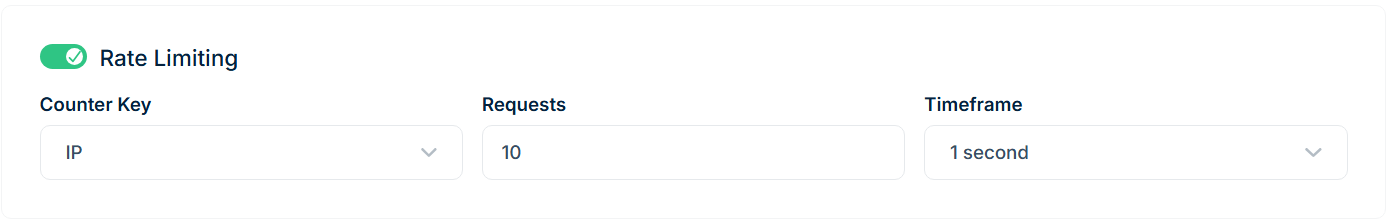
Apply rate limits where they matter
Not every endpoint behaves the same way, so protection shouldn’t be uniform.
Some routes are public and inexpensive. Others are sensitive or resource-intensive. Applying a single rate limit across an entire API rarely reflects how real systems behave.
API Guardian allows you to define rate limits per endpoint, aligned directly with your API structure.
Path templates such as
/users/{id}
work out of the box, so you don’t need to define rules for every variation. Rate limits are applied at the template level, meaning all variations of a route share the same counter by default.
You can define limits globally per endpoint or per IP address, with time windows ranging from one second to one hour. Versioned endpoints such as
/v1
and
/v2
are treated independently, allowing you to tune protection as your API evolves.
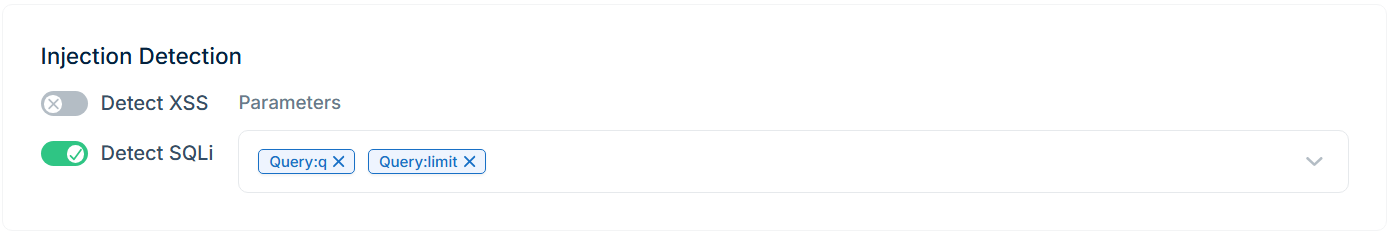
Combine structure with targeted protection
Schema validation ensures requests are structurally correct, based on your API schema. Some behaviors still fall outside structure alone.
API Guardian allows you to apply targeted injection detection to specific parameters. You can choose which query, path, header, or cookie values should be inspected for patterns like XSS or SQL injection.
This combines schema validation with traditional WAF protection, giving you precise control over where deeper inspection is applied.
Built into the edge, not added on top
API Guardian runs directly within the bunny.net edge as part of the existing request pipeline.
Validation happens in the same path as the rest of Bunny Shield, so requests don’t take an extra hop. This keeps latency low while filtering invalid traffic before it reaches your origin, acting as a first layer of protection for APIs that would otherwise need to handle this traffic themselves.
Availability and limits
API Guardian is currently in public preview on Bunny Shield Advanced plans and above.
We designed a simple, tiered structure to match the needs of different teams: Advanced and Business plans include clear endpoint limits, while Enterprise offers full customization. This keeps things straightforward and focused.
Endpoint limits scale by plan:
- Advanced: up to 10 endpoints
- Business: up to 50 endpoints
- Enterprise: customizable based on your needs
We set these limits intentionally. Rather than encouraging blanket protection across every single endpoint (which often leads to noise and maintenance overhead), we want to help teams focus on securing their highest-traffic, most sensitive, and business-critical endpoints.
API Guardian currently supports OpenAPI 3.0.x specifications.
You can re-upload and evolve your schema at any time. Existing endpoints retain their configuration, while removed endpoints are automatically cleaned up.
What’s next for Bunny Shield
API Guardian completes the initial vision for Bunny Shield, bringing structure and intent into how traffic is evaluated at the edge.
From here, the focus shifts to refining and expanding what’s already there. That includes improving existing protections, advancing bot detection to better handle modern traffic patterns, and continuing to evolve the platform based on real-world usage and feedback.
Because bunny.net sits at the edge, our global network acts as your first and strongest line of defense. We designed Bunny Shield to secure all your workloads, from website traffic and APIs to AI models, stopping attacks before they ever hit your servers. We have an exciting roadmap ahead.
Start protecting your API contract
Getting started is straightforward.
Upload your OpenAPI schema, refine validation, and apply authentication and rate limits per endpoint.
Start in log mode, observe what your API actually receives, then switch to blocking once you're confident.
Security shouldn’t require complex rules or constant tuning. With API Guardian, your API contract becomes the source of truth.
Log in or sign up to upload your schema and start protecting your API.